What is Cybersecurity? Everything You Need to Know

What is Cybersecurity- Cybersecurity is the security of internet-connected systems, including hardware, software, as well as data, from cyber threats. Individuals and businesses use the method to prevent illegal access to data centers as well as other digital systems.
A strong cybersecurity strategy provides a better security posture against hostile attacks aimed at gaining access to, altering, deleting, destroying, or extorting critical data from an organization’s or user’s systems. Cybersecurity is also important in preventing attacks that try to disrupt or interrupt the performance of a system or device.
What is the significance of cyber security?
The significance of cybersecurity keeps growing as the number of people, devices, and programs in the modern company grows, along with the rising data deluge, most of which is important or confidential. The problem is exacerbated by the increasing number and sophistication of cyber attackers as well as attack strategies.
Elements of Cybersecurity and Its Works-
The cybersecurity area is divided into numerous sections, each of which must be coordinated inside the company for a cybersecurity program to be successful. The following are included in these sections:
- Application security
- Information or data security
- Network security
- Operational security
- Cloud Security
- Critical infrastructure security
- Physical security
- End-user education
- Disaster recovery/business continuity planning
Managing cybersecurity in an ever-changing threat landscape is a difficult task for any company. Traditional reactive strategies, which focused resources on defending systems against the most well-known attacks while leaving lesser-known dangers undefended, are no longer sufficient.
A more proactive and flexible approach is required to stay up with shifting security dangers. Several important cybersecurity advice programs can help. To guard against known and unexpected risks, the National Institute of Standards and Technology (NIST) suggests using continuous monitoring as well as real-time assessments as part of the risk evaluation approach.
Benefits of Cybersecurity
The following are some of the advantages of developing and sustaining cybersecurity practices:
- Cybersecurity and data breach protection for businesses.
- Information and network security are both protected.
- Unauthorized user access is avoided.
- After a breach, there is a faster recovery time.
- End-user as well as endpoint device protection.
- Regulatory adherence.
- Continuity of operations.
- Developers, partners, consumers, stakeholders, and workers have more faith in the company’s reputation and trust.
Types of Cybersecurity Threats-
It’s a difficult task to stay up with new technology, security trends, as well as threat intelligence. It’s required to safeguard data and other assets against cyber threats, which can take numerous forms. The following are examples of cyber threats:
Malware
Any file or program can be used to damage a computer user with this type of malicious software. Worms, viruses, Trojan horses, and malware are examples of this.
Ransomware
It’s a different form of malware. It occurs when an attacker encrypts and locks the victim’s device system files as well as demanding cash to decrypt & unlock them.
Social engineering
It’s a type of attack that uses human interaction to persuade users to break security processes in order to obtain access to sensitive information that is normally protected.
Phishing
It’s a type of social engineering in which phony email or text messages are delivered that look like they came from a credible or well-known source. The goal of these communications, which are frequently random, is to collect sensitive data, like credit card or login information.
Spear phishing
It’s a form of phishing assault that targets a specific user, company, or organization.
Insider Threats
Humans, whether as employees, contractors, or customers, are responsible for security vulnerabilities or losses. Insider dangers can be either malicious or careless.
Distributed denial-of-service (DDoS) attacks
Multiple systems affect the traffic of a targeted device, such as a server, webpage, or other network device, in these attacks. Attackers can slow or damage the target system by overloading it with messages, connection requests, or packets, preventing genuine traffic from accessing it.
Advanced persistent threats (APTs)
These are long-term targeted attacks in which an attacker penetrates a network and goes undiscovered for a long time in order to steal the data.
Man-in-the-middle (MITM) attacks
These are eavesdropping attacks in which an attacker intercepts and transmits messages between 2 parties who think they are in communication.
Botnets, drive-by-download attacks, exploit kits, malvertising, vishing, credential stuffing assaults, cross-site scripting (XSS) attacks, SQL injection attacks, business email compromise (BEC), as well as zero-day exploits are all examples of typical attacks.
Top Cybersecurity challenges-
Hackers, data loss, privacy, risk management, as well as changing cybersecurity methods are all constant threats to cybersecurity. The frequency of cyberattacks is unlikely to reduce very soon. Furthermore, additional attack access points, such as the Internet of Things (IoT), raise the need for computer and network security.
The ever-changing nature of security vulnerabilities is one of the most difficult aspects of cybersecurity. New attack channels emerge as new technologies emerge and as technology is exploited in new or different ways.
It can be difficult to keep up with the constant changes and advancements in assaults, as well as to update practices to protect against them. Among the issues is ensuring that all aspects of cybersecurity are kept up to date in order to secure against security flaws. Smaller businesses without staff or in-house resources may find this particularly tough.
Furthermore, organizations can collect a wealth of information about individuals who utilize one or more of their products. The likelihood of a cybercriminal attempting to steal personally identifiable information (PII) increases as more data is collected. An organization that saves PII on the cloud, for example, could be the target of a ransomware assault. Organizations should do all possible to avoid a cloud compromise.
Employees may bring malware into the office on their laptops or mobile devices, thus cybersecurity strategies should include end-user education. Employees who receive regular security awareness programs will be better able to contribute to keeping their firm safe from cyber threats.
Another issue with cybersecurity is a scarcity of competent cybersecurity professionals. As businesses acquire and use more data, the demand for cybersecurity professionals to assess, manage, and respond to problems grows. The workplace gap among necessary cybersecurity jobs as well as security specialists, according to (ISC)2, is expected to reach 3.1 million.
Role of Automation in Cybersecurity-
Automation has become a critical component in ensuring that businesses are protected from the increasing number as well as the severity of cyber threats. In regions with high-volume data streams, artificial intelligence (AI) as well as machine learning can improve overall cybersecurity in three ways:
Detection of threats
AI platforms can examine data and detect and predict known and unknown risks.
Response to a threat
Security protections are also created and implemented automatically by AI platforms.
Augmentation of humans
Security professionals are sometimes overburdened with alerts and routine tasks. AI can help to minimize alert fatigue by automatically triaging low-risk warnings as well as automating big data analysis as well as other repetitive operations, freeing humans to focus on more complex duties.
Attack categorization, malware classification, traffic analysis, compliance analysis, and much more are all positives of automation in cybersecurity.
Cybersecurity Tools-
Cybersecurity vendors often offer a wide range of security products and services. The following are examples of common security tools and systems:
- Identity and access management (IAM)
- Firewalls
- Endpoint protection
- Antimalware
- Intrusion prevention/detection systems (IPS/IDS)
- Data loss prevention (DLP)
- Endpoint detection and response
- Security information and event management (SIEM)
- Encryption tools
- Vulnerability scanners
- Virtual private networks (VPNs)
- Cloud workload protection platform (CWPP)
- Cloud access security broker (CASB)
Career opportunities in cybersecurity-
Persons with cybersecurity awareness as well as hardware and software capabilities are in demand as the cyberthreat landscape is constantly changing and new dangers arise, such as IoT risks.
Security positions require IT professionals and other computer skills, such as:
Chief information security officer (CISO)
The CISO is the person in charge of implementing the security program across the firm and overseeing the operations of the IT security department.
Chief Security Office (CSO)
The CSO is the executive in charge of a company’s physical and/or cybersecurity security.
Security engineers
They focus on quality management within the IT infrastructure to protect company assets from attacks.
Security architects
They are in charge of an organization’s essential infrastructure planning, analysis, design, testing, maintenance, and support.
Security analysts
Planning security procedures and controls, securing digital files, and conducting both internal and external security audits are among their tasks.
Penetration testers
They’re ethical hackers who look for vulnerabilities in systems, networks, and applications that could be abused by bad actors.
Threat hunters
They are threat analysts whose job is to find as well as mitigate vulnerabilities and threats before they compromise a company.
Security consultants, data protection officers, cloud security architects, security operations management (SOC) managers and analysts, security investigators, cryptographers, as well as security administrators are among the other cybersecurity occupations.
- What is Cybersecurity Threats?
- How war shifted the plans of one Ukrainian Cybersecurity Entrepreneur
People May Ask
What is cybersecurity?
Cyber security What is it- The technique of protecting computers, servers, mobile devices, electronic systems, networks, as well as data from hostile intrusions is known as cyber security. It’s also known as electronic data security or information technology safety. The phrase is used in a range of contexts, ranging from business to mobile computing, and it may be broken down into a few categories.
- Network security
- Information security
- Application security
- Operational security
- Disaster recovery and business continuity
- End-user education or training
What Is Internet Security?
The management of cyber hazards and dangers linked with the Internet, online browsers, web apps, websites, and networks is a major part of Internet security. The major goal of Internet security solutions is to safeguard consumers and business IT assets against Internet-based threats.
What are the five different types of cyber security?
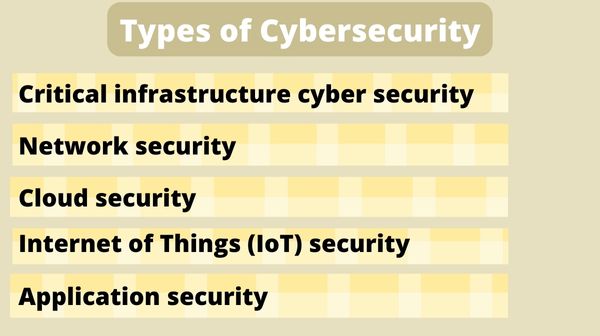
Critical infrastructure cyber security
Because SCADA (supervisory control as well as data acquisition) systems usually depend on older software, major infrastructure companies are more susceptible to attack than others.
The NIS Regulations apply to operators of vital services in the UK’s energy, transportation, health, water, as well as digital infrastructure sectors, as well as digital service providers.
The Regulations, among other things, require businesses to take suitable technical and organizational steps to control their security risks.
Network security
Addressing vulnerabilities in your operating systems and network architecture, such as servers and hosts, firewalls as well as wireless access points, as well as network protocols, is part of network security.
Cloud Security
The security of data, apps, as well as infrastructure in the cloud is the focus of cloud security.
Internet of Things (IoT) security
IoT security refers to the protection of smart devices and networks that are connected to the Internet of Things. Smart fire alarms, lighting, thermostats, and other appliances are examples of IoT devices that connect to the Network without the need for human involvement.
Application security
Addressing vulnerabilities originating from unsafe development processes in the design, coding, and publication of software or a website is what application security is all about.